Category: WordPress
-
Adding an MCP Server to the WordPress Core Development Environment
How I’ve enabled Claude Code to access all abilities registered with the Abilities API via MCP in the wordpress-develop environment.
-
Post Date Block: Published & Modified

Development of a WordPress plugin which appends the modified date to the Post Date block when it is different from the published date.
-
WordPress 6.9 Performance Landings
Celebrating the performance improvements in the latest release, and reflecting on the effort to make it happen.
-
The Site Speed Frontier with Performance Lab and Beyond
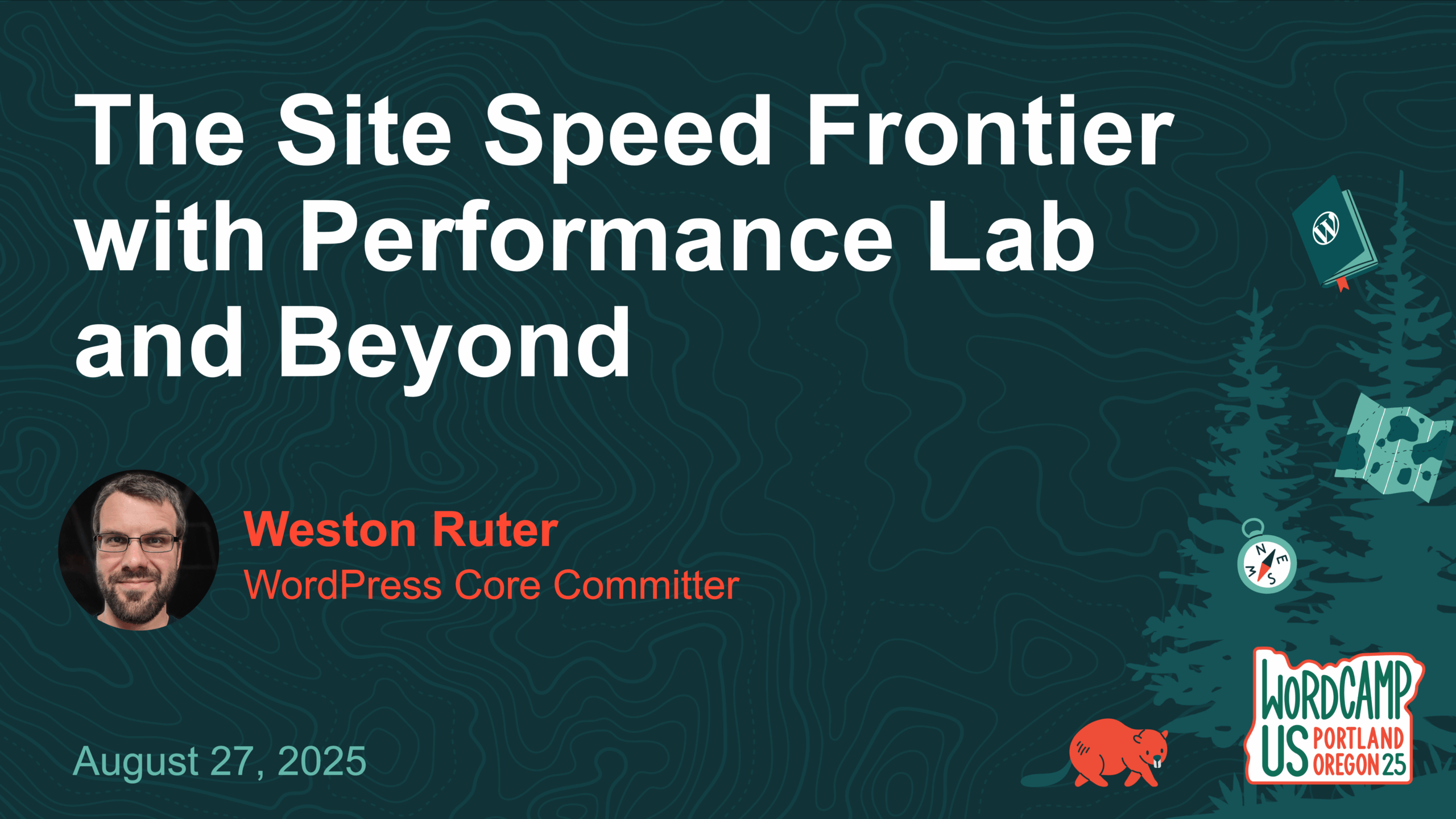
Analysis of the LCP impact for optimizations featured by the Performance Lab plugin and proposed for WordPress core. Presented at WCUS 2025.
-
Web Performance Milestone
A couple months ago, this blog reached a web performance milestone which I shared on LinkedIn, Bluesky, Mastodon, Twitter: For the first time ever, I’ve just seen my blog appear in field metrics from CrUX (Chrome UX Report), albeit in desktop only and for the origin not an individual URL. Baby steps. In any case,…
-
Instant Back/Forward Navigations in WordPress
The new Instant Back/Forward plugin enables instant navigations in the browser history via the bfcache, particularly while logged in.
-
Eliminating Layout Shifts in the Video Block

Like the rest of the internet, I’ve been awestruck by the quality of Google’s Veo 3 AI video generator (even with audio). As you’ve seen from my posts, the American bison 🦬 is my favorite animal (aside from my cat of course). Also, perhaps I’ve watched too many videos from the Mustache Farmer, but I…
-
Improve LCP by Deprioritizing Script Modules from the Interactivity API

Adding a fetchpriority of low to script modules and moving them from the head to the footer can improve LCP by >9%! I’ve written plugins you can use to implement this now while waiting for them to land in WordPress core.
-
Adding Caption & Lightbox to the Featured Image Block

Earlier this year I re-built this site using the Twenty Twenty-Five theme, finally adopting a block theme over the veritable Twenty Twenty classic theme I had been using. In this rebuild, one thing that I had trouble with is the featured image. In the Twenty Twenty theme, a caption is rendered under the featured image…
-
A Decade as a Core Committer: My WordPress Contribution History

Next Tuesday is my 10-year anniversary of becoming a WordPress core committer back on May 20, 2015. This post is somewhat of a résumé for my contributions to the WordPress project. I joined Google in 2018 to work full time on WordPress. After 6½ years, my sponsored contributor position there has been eliminated. I’m hoping…